Radio Frequency Identification (RFID) technology has seamlessly woven itself into the fabric of modern life, powering everything from contactless payments and inventory management to access control and supply chain tracking. At the heart of every RFID system lies the RFID reader, a sophisticated device that acts as the bridge between the physical world of tagged objects and the digital world of data processing. But how exactly does this seemingly magical device work? This article will demystify the inner workings of RFID readers, exploring their components, operational principles, communication protocols, and real-world applications, all supported by relevant data and practical insights.
The Core Components of an RFID System
Before delving into the reader’s mechanics, it’s essential to understand the basic architecture of an RFID system, which comprises three fundamental elements:
- The Tag (or Transponder): This is the small device attached to the object being tracked. It contains a microchip for storing data (like a unique ID) and an antenna for receiving and transmitting radio waves. Tags can be passive (powered by the reader’s signal), active (with their own battery), or semi-passive (battery-powered but using the reader’s signal for communication).
- The Reader (or Interrogator): This is the “brain” of the operation. Its primary function is to generate a radio frequency (RF) field, communicate with tags within that field, read the data from them, and often write new data to them. It then sends this information to a host computer system for processing.
- The Antenna: This component is physically connected to the reader and is responsible for emitting the RF energy to power passive tags and for sending and receiving signals to and from the tags. A single reader can be connected to multiple antennas to cover a larger area.
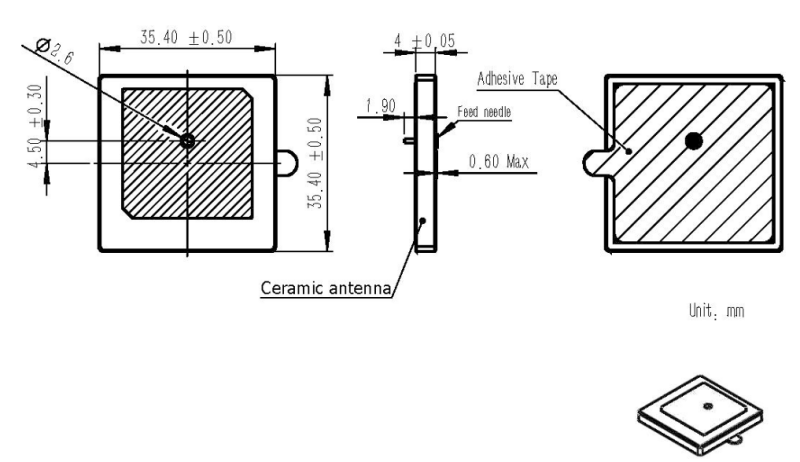
The 36MM UHF Ceramic Antenna (902–928MHz) is specifically designed to deliver stable short-to-medium range performance, compact integration, and high read accuracy in RFID and IoT systems.
In many commercial devices, the reader’s internal electronics (transmitter, receiver, and microprocessor) are packaged together in a single unit, with the antenna either integrated or connected externally.
The Working Principle: A Dance of Energy and Data
The operation of an RFID reader, especially with the most common passive tags, is a fascinating two-way interaction based on the principles of electromagnetic coupling. Here’s a step-by-step breakdown of the process:
1. Generating the Electromagnetic Field
The process begins when the reader, powered by its own source, activates its transmitter circuit. This circuit generates an alternating current at a specific radio frequency. This current flows through the reader’s antenna, which converts it into an oscillating electromagnetic field that radiates outwards into the surrounding space. The strength and reach of this field depend on the reader’s power output and the frequency band it operates in.
2. Powering the Passive Tag
When a passive RFID tag enters this electromagnetic field, its own antenna—essentially a coil of wire—captures some of this RF energy. Through the principle of electromagnetic induction (similar to how a transformer works), this captured energy induces a small electrical current in the tag’s antenna. This induced current is then rectified and used to power the tiny integrated circuit (IC) on the tag. This is the critical moment where the dormant tag “comes to life.”
3. Communication: Modulation and Backscatter
Once powered, the tag’s IC prepares to send its stored data back to the reader. However, the tag doesn’t have its own powerful transmitter. Instead, it uses a clever technique called backscatter modulation.
- The tag’s IC manipulates the electrical load connected to its antenna. By switching this load on and off in a specific pattern that corresponds to its digital data (e.g., a ‘1’ or a ‘0’), it changes the amount of energy it reflects back to the reader.
- When the load is high, more of the incoming RF energy is absorbed, and less is reflected.
- When the load is low, more energy is reflected back.
- This intentional variation in the reflected signal is the modulated data stream.
4. Receiving and Decoding the Signal
The reader’s antenna, now acting as a receiver, picks up this faint, modulated backscattered signal from the tag. The reader’s sensitive receiver circuit then amplifies this weak signal and demodulates it. Demodulation is the process of extracting the original digital data (the tag’s ID) from the carrier wave. The reader’s internal microprocessor then processes this data, checks for errors, and formats it for transmission.
5. Sending Data to the Host System
Finally, the reader communicates the decoded tag information to a backend computer system, often referred to as the host. This communication can happen over various interfaces like Ethernet, Wi-Fi, USB, or serial connections. The host system is where the real-world application logic resides—it might update an inventory database, open a security gate, or log an asset’s location.
This entire cycle, from powering the tag to receiving its data, happens in a fraction of a second, enabling rapid and efficient identification of multiple items.
Understanding Frequency Bands and Their Impact
RFID systems operate across several distinct frequency bands, each with its own set of characteristics, advantages, and ideal use cases. The choice of frequency fundamentally shapes how the reader and tag interact.
| Frequency Band | Common Name | Typical Range | Data Transfer Rate | Key Characteristics | Primary Applications |
|---|---|---|---|---|---|
| Low Frequency (LF) | 125 – 134 kHz | < 10 cm | Low (a few kbps) | Excellent penetration through water and metal; very short range; highly reliable in challenging environments. | Animal tracking, access control, car immobilizers. |
| High Frequency (HF) | 13.56 MHz | < 1 m | Moderate | Good balance of range and data rate; works well near water and metals; supports NFC (a subset of HF RFID). | Library books, payment cards (NFC), smart cards, tickets. |
| Ultra-High Frequency (UHF) | 860 – 960 MHz | Up to 12+ m | High | Longest read range; fastest data transfer; can read many tags simultaneously; performance degrades near water and metal. | Supply chain, retail inventory, logistics, pallet tracking. |
| Microwave | 2.45 GHz / 5.8 GHz | Several meters | Very High | Very high data rates; used for specialized, high-speed applications. | Toll collection (ETC), high-speed vehicle tracking. |
For instance, a UHF reader in a warehouse can quickly scan hundreds of tagged boxes on a pallet from several meters away, making it ideal for bulk inventory. In contrast, an LF reader on a farm can reliably read a tag embedded in an animal’s ear, even though the tag is surrounded by water-rich tissue, a scenario where UHF would fail.
Managing the Crowd: Anti-Collision Protocols
In real-world scenarios, a single reader’s field often contains multiple tags. If all these tags tried to respond to the reader at the same time, their signals would collide, creating unreadable noise—a problem known as the “tag collision” problem. To solve this, RFID systems employ sophisticated anti-collision protocols. The two most common types are:
- ALOHA-based Protocols: These are probabilistic. Tags respond to the reader’s query at random intervals. If a collision is detected, the reader instructs the tags to try again after another random delay. This method is simple and fast when there are only a few tags but becomes inefficient as the number of tags increases.
- Tree-walking (or Binary Tree) Protocols: This is a deterministic approach. The reader systematically queries tags by asking about specific bits of their unique ID. For example, it might first ask, “All tags whose ID starts with a ‘0’, please respond.” If a collision occurs, it drills down further (“All tags whose ID starts with ‘01’…”). This method is more efficient for large populations of tags but can be slower for small groups.
Modern UHF readers often use advanced variants of these protocols, such as the Q-algorithm (an adaptive form of slotted ALOHA defined in the ISO/IEC 18000-63 standard), which dynamically adjusts its parameters based on the number of tags it detects, optimizing for speed and efficiency.
Performance Metrics That Matter: Read Range, Throughput, and Accuracy
The theoretical promise of RFID is only realized when the system performs reliably in the real world. Selecting an RFID reader based solely on its price or brand is a recipe for failure. Instead, decision-makers must focus on three core performance metrics—read range, throughput, and accuracy—as these directly determine whether an RFID solution will meet its operational objectives. These metrics are not static; they are profoundly influenced by environmental conditions, tag selection, and reader configuration.
1. Read Range: The Reach of the RF Field
Read range is the maximum distance at which a reader can successfully power a passive tag and receive its data. It is perhaps the most advertised—but also the most misunderstood—specification.
- Theoretical vs. Real-World Range: Manufacturers often quote “maximum read range” under ideal laboratory conditions (e.g., an open field with a high-performance tag and no interference). In practice, the effective range can be drastically reduced.
- Key Influencing Factors:
- Frequency: UHF offers the longest range (up to 12+ meters), while HF is limited to about 1 meter, and LF to just centimeters.
- Tag Design: A tag’s antenna size, chip sensitivity, and orientation relative to the reader’s antenna are critical. A large, linearly-polarized tag aligned with the reader will perform far better than a small, circularly-polarized one at an odd angle.
- Environment: Water (including the human body) absorbs UHF signals, and metal reflects them, both causing significant signal loss or null zones. A tag on a bottle of water may have a range of only 30 cm, even with a powerful reader.
- Regulatory Power Limits: Legal restrictions on transmit power vary by region (e.g., 30 dBm in North America vs. 27 dBm in Europe), capping the maximum achievable range.
A 2024 benchmark study by the ARC Advisory Group tested a leading UHF reader (Impinj Speedway R700) with a common retail tag (Alien ALN-9640) in a controlled warehouse environment. The results highlight the gap between theory and reality:
| Environment | Max Read Range (Meters) | Notes |
|---|---|---|
| Open Field (Ideal) | 15.2 | No obstacles, perfect tag alignment |
| Standard Warehouse | 8.5 | Minor obstructions, mixed tag orientations |
| Near Metal Shelving | 3.1 | Significant signal reflection/interference |
| On Liquid-Filled Box | 2.7 | Signal absorption by water content |
This data underscores the necessity of conducting a Proof-of-Concept (PoC) test in the actual deployment environment before finalizing hardware.
2. Throughput: Speed of Data Capture
Throughput measures how quickly a reader can identify and process a population of tags. It is typically expressed in tags per second and is crucial for high-speed applications like conveyor belt sorting or vehicle tolling.
- Protocol Dependency: Throughput is heavily dependent on the anti-collision protocol used. Advanced protocols like the Q-algorithm in EPC Gen2v2 can achieve read rates of over 1,000 tags per second under optimal conditions.
- Reader Processing Power: High-end fixed readers have dedicated processors to handle the complex signal processing required for fast, simultaneous reads, whereas lower-cost or handheld units may be slower.
- Tag Density: Counterintuitively, throughput can decrease in extremely dense environments if the anti-collision algorithm becomes overwhelmed, leading to repeated collisions and retries.
For example, in a modern e-commerce fulfillment center, a high-throughput reader on a packing chute must reliably read every item in a box within a fraction of a second as it moves past at high speed. A throughput of less than 200 tags/sec could become a bottleneck in such a scenario.
3. Read Accuracy: The Foundation of Trust
Accuracy is the percentage of tags in a read zone that are successfully and correctly identified by the reader. A system with poor accuracy generates false negatives (missed tags) and false positives (ghost reads), eroding user trust and potentially causing costly errors like shipping the wrong inventory.
- Defining Accuracy: In a controlled test of 100 tagged items, if the reader reports 98 unique, correct IDs, its read accuracy is 98%. An accuracy rate below 95% is often considered unacceptable for critical business processes.
- Sources of Inaccuracy:
- Multipath Fading: RF signals bouncing off walls and metal objects can create dead zones where the signal cancels itself out.
- Tag-to-Tag Interference: Tags placed too close together can detune each other’s antennas, reducing their ability to respond.
- Insufficient Dwell Time: If a tag is moving through the read zone too quickly (e.g., on a fast conveyor), the reader may not have enough time to complete the communication handshake.
GS1, the global standards organization, recommends that for supply chain applications, RFID systems should be designed and tuned to achieve a minimum read accuracy of 99% during operational use. Achieving this requires careful planning of antenna placement, polarization, and reader power settings.
Synthesizing the Metrics for Success
These three metrics are interdependent. Increasing read power might extend range but could cause more tag collisions, reducing throughput and accuracy. Using a higher-gain antenna can boost range but creates a narrower, more focused beam, which might miss tags outside its tight coverage area.
Therefore, the key to a successful deployment is not to maximize any single metric in isolation, but to optimize the balance among all three for the specific application. This requires a systematic approach:
- Define Requirements: What is the minimum required range? What is the target tag population and speed? What accuracy level is acceptable?
- Conduct Environmental Analysis: Map out sources of interference (metal, water, other RF devices).
- Perform Rigorous Testing: Use a variety of tags and reader configurations in the actual environment to find the optimal setup.
By grounding decisions in these concrete performance metrics, organizations can move beyond speculation and build RFID systems that deliver consistent, reliable, and valuable results.
Security and Privacy Concerns in RFID Systems
While RFID technology offers immense benefits in automation and tracking, its wireless nature introduces significant security and privacy vulnerabilities that must be addressed. Unlike barcodes, which require line-of-sight scanning, RFID tags can be read silently and at a distance, potentially without the knowledge or consent of the individual carrying them. This section explores the primary threats, established countermeasures, and practical guidance for secure deployment.
Common Security Threats
RFID systems are susceptible to several well-documented attacks:
- Eavesdropping (Skimming): An unauthorized reader can intercept the communication between a legitimate reader and a tag. Since many basic RFID protocols transmit data in plaintext, an attacker can easily capture sensitive information like a unique ID or even payment credentials.
- Unauthorized Tag Cloning: Once an attacker has skimmed a tag’s data, they can program a blank tag with the same information, effectively creating a clone. This cloned tag can then be used to gain illegitimate access or make fraudulent transactions.
- Denial-of-Service (DoS): An attacker can flood the operating frequency band with noise, preventing legitimate readers from communicating with tags. Alternatively, they can exploit protocol weaknesses to permanently disable a tag using a “Kill” command if it is not properly secured.
- Tracking and Profiling: The unique identifier on a tag can be used to track the movement of an object or, more invasively, a person. For example, a store could track a customer’s path through the store by reading the RFID tags in their clothing, building a detailed profile of their shopping habits without explicit consent.
A 2025 industry report on Industrial IoT security highlighted that over 60% of legacy RFID deployments in supply chain management lacked any form of cryptographic authentication, making them highly vulnerable to cloning and data theft.
Security Mechanisms and Protocols
To combat these threats, various security mechanisms have been developed and standardized. The level of security is often tied to the specific RFID protocol in use.
| Protocol / Standard | Frequency | Typical Use Case | Security Features | Key Vulnerabilities |
|---|---|---|---|---|
| ISO/IEC 14443 | HF (13.56 MHz) | Payment cards, e-passports, access control | Supports mutual authentication, strong encryption (e.g., 3DES, AES), and secure messaging. NFC is built on this standard. | Older implementations (e.g., MIFARE Classic) had broken crypto; newer versions (MIFARE DESFire) are robust. |
| ISO/IEC 15693 | HF (13.56 MHz) | Library books, asset tracking | Optional password-based protection for memory blocks. Generally less secure than ISO 14443. | Passwords are often short and transmitted in the clear, making them easy to brute-force. |
| EPC Gen2 (ISO/IEC 18000-63) | UHF (860-960 MHz) | Supply chain, retail inventory | Features a 32-bit “Access Password” to protect write/lock commands and a “Kill Password” to permanently disable a tag. Newer versions (Gen2v2) add cryptographic support. | The standard Access Password is often left at its default value (0x00000000) or set to a weak, predictable value, rendering it useless. |
The evolution from EPC Gen2 to Gen2v2 (also known as ISO/IEC 18000-64) was a direct response to security concerns. Gen2v2 mandates support for cryptographic suites, enabling true authentication and encrypted communication, which is crucial for applications handling sensitive data.
Practical Recommendations for Secure Deployment
For organizations implementing RFID, a proactive security strategy is essential:
- Never Rely on Obscurity: Assume that an attacker knows your system’s design. Security should be based on strong cryptography, not on the secrecy of the protocol.
- Enforce Strong Passwords: For UHF systems using EPC Gen2, always change the default Access and Kill passwords to long, random, and unique values. Manage these keys securely in a dedicated key management system.
- Choose the Right Protocol for the Risk: For high-security applications like payments or identity verification, mandate the use of ISO/IEC 14443-compliant tags with certified cryptographic capabilities (e.g., NXP’s MIFARE DESFire EV3).
- Implement Physical and Logical Controls: Use shielding materials (e.g., wallets with Faraday cages) to block unwanted reads of personal items. On the network side, ensure that data from RFID readers is transmitted over encrypted channels (e.g., TLS) to the backend system.
- Follow Industry Guidelines: Adhere to best practices from authoritative bodies like the National Institute of Standards and Technology (NIST) and GS1, which provide detailed frameworks for securing RFID-enabled applications.
In conclusion, while RFID security challenges are real, they are not insurmountable. By understanding the threat landscape and deploying appropriate technical and procedural safeguards, businesses can harness the power of RFID while protecting their assets and their customers’ privacy.
Real-World Applications and Market Impact
The versatility of RFID readers has driven their adoption across a staggering array of industries. The global market for RFID technology is a testament to its value. According to industry analyses, the market for RFID-integrated smart packaging alone was valued at $5.2 billion in 2025 and is projected to reach $15.6 billion by 2035, growing at a compound annual growth rate (CAGR) of 11.9%. This explosive growth is fueled by the need for greater supply chain visibility, anti-counterfeiting measures, and enhanced consumer engagement.
- Retail: Major retailers like Zara and Uniqlo use UHF RFID for real-time inventory management. A simple scan of a fitting room or a shelf can provide an instant stock count, reducing out-of-stocks and improving the customer experience. View related products: 165MM 4dbi RFID UHF Reader Antenna For Warehouse Management
- Logistics & Supply Chain: From manufacturing floors to distribution centers, RFID readers track goods in transit. A pallet of goods can be verified as it leaves a dock, ensuring the right shipment goes to the right place without manual scanning. View related products: 12dBi Circular UHF Reader Antenna For RFID logistics tracking
- Healthcare: Hospitals use HF RFID to track high-value medical equipment, manage pharmaceutical inventory, and even ensure patient safety by matching patients to their correct medication.
- Access Control & Security: From key fobs for building entry to passports with embedded RFID chips, readers provide a secure and convenient way to verify identity.
Reader Deployment Strategies: Fixed vs. Handheld vs. Integrated
Selecting the right RFID reader type is a critical strategic decision that directly impacts the efficiency, cost, and scalability of an RFID deployment. The three primary categories—fixed, handheld, and integrated readers—each serve distinct operational needs. Understanding their unique characteristics, advantages, and limitations is essential for designing a system that delivers maximum return on investment.
Fixed Readers: The Backbone of Automated Processes
Fixed RFID readers are permanently installed at strategic points within a facility to enable hands-free, continuous monitoring and data capture. They are typically connected to multiple high-gain antennas to create a defined read zone.
- Key Characteristics:
- High Performance: Designed for 24/7 operation with robust processing power to handle high tag volumes and complex anti-collision protocols.
- Scalability: A single fixed reader can manage up to 8 or more antennas (via antenna multiplexers), allowing coverage of large areas like dock doors, conveyor belts, or warehouse aisles.
- Integration: Seamlessly connects to enterprise systems (WMS, ERP) via Ethernet, Wi-Fi, or industrial protocols (e.g., Modbus TCP).
- Ideal Use Cases:
- Receiving/Shipping Docks: Automatically verifying inbound/outbound pallets against shipping manifests.
- Conveyor Systems: Tracking items in real-time as they move through production or sorting lines.
- Access Control Points: Monitoring the movement of assets or personnel through secure portals.
According to a 2025 market analysis by ABI Research, fixed UHF readers account for over 70% of all RFID reader revenue in industrial and logistics settings, underscoring their role as the workhorse of large-scale automation.
View related products: Industrial UHF RFID Fixed Reader Manufacturer 8 Ports Long Range
Handheld Readers: Flexibility for On-Demand Tasks
Handheld RFID readers are portable, battery-powered devices that combine a reader, antenna, and often a small computer (with a screen and keypad) into a single mobile unit. They offer unparalleled flexibility for tasks that are not confined to a single location.
- Key Characteristics:
- Mobility & Agility: Empowers workers to perform inventory counts, asset audits, or item searches anywhere in a facility without being tethered to a fixed point.
- User Interaction: Built-in displays and interfaces allow for immediate data verification and action (e.g., marking an item as found or damaged).
- Connectivity: Modern handhelds feature Wi-Fi, Bluetooth, and cellular connectivity for real-time data synchronization with backend systems.
- Ideal Use Cases:
- Cycle Counting in Retail: Quickly scanning shelves to reconcile physical inventory with system records.
- Field Service & Maintenance: Locating and verifying specific tools or spare parts in a large storage yard or on a job site.
- Event Management: Checking in attendees or managing equipment rentals at conferences or festivals.
While their per-unit cost is lower than a fixed reader setup, their value lies in labor savings. A study by VDC Research found that organizations using handheld RFID readers for inventory management reported an average 35% reduction in time spent on manual stock checks compared to traditional barcode scanning.
View related products: DO RFID Reader Factory UHF Android Handheld RFID Reader High Performance
Integrated Readers: Embedding Intelligence into Devices
Integrated RFID readers are compact modules designed to be embedded directly into other machines, kiosks, or OEM products. They provide RFID functionality without requiring a standalone reader unit.
- Key Characteristics:
- Compact Form Factor: Small PCB modules that can be easily incorporated into the design of a larger product.
- OEM Focus: Sold to manufacturers who build them into their own solutions, such as smart shelves, medical devices, or self-checkout kiosks.
- Simplified Interface: Communicate with the host device’s main processor via simple serial (UART) or USB interfaces.
- Ideal Use Cases:
- Smart Retail Shelving: Shelves that can detect when a product is removed or restocked, triggering automatic replenishment alerts.
- Medical Device Management: Infusion pumps or surgical trays that automatically log their usage and location when placed on a designated station.
- Library Self-Checkout Kiosks: Allowing patrons to check out multiple books at once by placing them on a built-in RFID pad.
This category represents a growing segment of the market, driven by the demand for smarter, connected devices in the Internet of Things (IoT) ecosystem.
Comparative Overview and Selection Guidance
The table below summarizes the key differences to aid in the selection process:
| Feature | Fixed Reader | Handheld Reader | Integrated Reader |
|---|---|---|---|
| Primary Advantage | Automation, High Throughput | Mobility, Flexibility | Embedded Functionality |
| Typical Cost Range | $1,000 – $5,000+ | $1,500 – $4,000 | $100 – $500 (module cost) |
| Read Range | Up to 12+ meters (UHF) | 1 – 10 meters (UHF) | < 1 meter (HF/UHF) |
| Power Source | AC Mains | Rechargeable Battery | Host Device Power |
| Best For | High-volume, static processes | Ad-hoc, mobile tasks | OEM product enhancement |
Practical Recommendation: A successful RFID strategy often involves a hybrid approach. For example, a large distribution center might use fixed readers at its loading docks for automated shipment verification, while its inventory team uses handheld readers for periodic audits and locating misplaced items. Meanwhile, its retail partners might deploy integrated readers in smart fitting rooms to enhance the customer experience. The key is to match the reader type to the specific workflow it is intended to support.
Conclusion and Practical Recommendations
Understanding how RFID readers work reveals a blend of elegant physics and smart engineering. They are not mere scanners but complex communication hubs that orchestrate a silent, invisible dialogue with the objects around us.
For businesses considering RFID implementation, the following practical advice is crucial:
- Choose the Right Frequency: Don’t default to UHF just because it has the longest range. If your environment is full of liquids or metals, LF or HF may offer far more reliable performance.
- Consider the Entire System: The reader is only one part. Invest time in selecting the appropriate tags, antennas, and middleware software that can effectively manage and interpret the data.
- Plan for Anti-Collision: If you need to read many tags at once, ensure your chosen reader and tags support a robust anti-collision protocol suitable for your expected tag density.
- Think About Integration: The true value of RFID is unlocked when its data is integrated into your existing business systems (ERP, WMS, etc.). Plan this integration from the outset.
As the Internet of Things (IoT) continues to expand, the role of the humble RFID reader will only become more central, quietly connecting our physical world to the vast digital networks that drive modern commerce and society.
DO RFID Reader
For organizations seeking a reliable, experienced, and customer-focused partner to bring their RFID vision to life, DO RFID Reader—a core manufacturing unit of D.O RFID Group—stands out as an ideal choice. With 14 years of dedicated expertise in the RFID and smart card industry, DO RFID Reader specializes in designing and producing high-quality RFID readers, NFC tags, RFID cards, and custom-engineered tags tailored for access control, vehicle identification, logistics, and inventory management systems worldwide.
Guided by the principle “Source Quality Products and Enjoy Efficient Service,” D.O RFID Group combines advanced manufacturing capabilities—including state-of-the-art Heidelberg printing technology—with a commitment to rapid delivery and long-term reliability. Every product comes with a 36-month warranty, backed by 24/7 technical support from seasoned engineers. As a trusted long-term supplier to major international projects (including Austria’s metro card system), DO RFID Reader has consistently demonstrated its ability to meet diverse global market demands with precision, flexibility, and integrity.
Whether you need standard UHF readers for warehouse automation or custom NFC-enabled tags for smart city applications, DO RFID Reader delivers innovation, quality, and service you can count on—at a fair price. Send email for more information.


